Why Supply Chain Cybersecurity and Vendor Risk Are Critical for African Businesses in 2026
Understanding Vendor Risk in African Supply Chains
As businesses navigate this landscape, managing vendor risk becomes increasingly crucial.
Managing vendor risk effectively is essential for maintaining a resilient supply chain.
Africa’s digital transformation is accelerating — but so are cyberattacks targeting procurement and supply chains. Criminals now exploit vendors, contractors, and third‑party systems because they are often the weakest link.
A single compromised supplier can expose:
- Procurement platforms
- Financial transactions
- Customer data
- Internal operations
- Entire supply chain networks
This makes supply chain cybersecurity a top priority for every organisation operating in Africa.
What Is Supply Chain Cybersecurity?
Supply chain cybersecurity refers to the strategies, controls, and technologies used to protect an organisation from cyber threats that originate from external partners, including:
Vendor Risk: Understanding the Importance for African Supply Chains
The focus on vendor risk cannot be overstated, as it is integral to overall cybersecurity strategies.
Addressing vendor risk helps strengthen the entire supply chain against possible threats.
Understanding vendor risk is vital for companies looking to protect their interests.
Strategies for Addressing Vendor Risk in Supply Chains
Importance of Supply Chain Cybersecurity in Vendor Management
How to Effectively Manage Vendor Risk in Your Supply Chain
Mitigating vendor risk not only protects your organisation but also enhances overall supply chain stability.
Mitigating vendor risk requires a comprehensive approach to security.
- Vendors
- Suppliers
- Contractors
- Logistics partners
- Technology providers
It ensures that every third‑party connected to your business does not become a gateway for cyberattacks.
Why African Supply Chains Are High‑Risk Targets
Vendor Risk: A Critical Element for Supply Chain Security
1. Weak Supplier Cyber Controls
Many African SMEs lack strong cybersecurity policies, making them easy entry points for attackers.
2. Rapid Digital Adoption Without Security
E‑procurement, cloud systems, and automation are growing — but security maturity is not.
H3: 3. High Exposure to Fraud & Impersonation
Invoice fraud, fake vendor schemes, and payment diversion attacks are increasing across the continent.
4. Low Cyber Awareness in Procurement Teams
Procurement staff are often targeted because they handle:
- Payments
- Supplier onboarding
- Sensitive documents
Monitoring vendor risk should be an ongoing process for businesses.
Common Cyber Threats in African Supply Chains
Vendor Impersonation Attacks
Cybercriminals create fake supplier profiles or emails to trick procurement teams into making payments.
Invoice Fraud & Payment Diversion
Attackers intercept or alter invoices, redirecting funds to fraudulent accounts.
If a supplier is hacked, attackers can access:
- Contracts
- Purchase orders
- Customer data
- Financial information
Procurement System Breaches
Weak access controls in e‑procurement platforms expose sensitive data.
How Cyberattacks Spread Through the Supply Chain
A single breach can:
- Infect connected systems
- Manipulate procurement data
- Disrupt operations
- Trigger financial losses
- Damage brand reputation
- Cause regulatory penalties
This is why third‑party cyber risk management is essential.
Essential Cybersecurity Controls for Procurement Teams
1. Supplier Verification & Due Diligence
Verify supplier identity, ownership, and cybersecurity maturity before onboarding.
2. Multi‑Factor Authentication (MFA)
All procurement systems must require MFA to prevent unauthorised access.
3. Cybersecurity Clauses in Contracts
Contracts should include:
- Data protection requirements
- Incident reporting timelines
- Minimum security standards
4. Cyber Awareness Training for Procurement Teams
Teams must be trained to detect:
- Phishing
- Fake vendors
- Suspicious invoices
- Social engineering
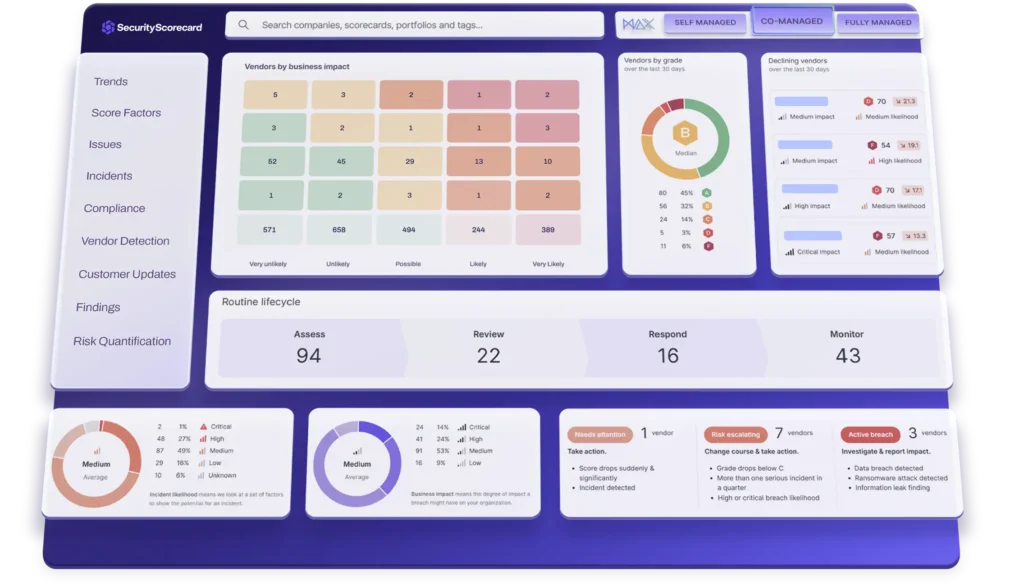
5. Continuous Monitoring of Supplier Cyber Risk
Cyber risk is dynamic — suppliers must be monitored continuously.
Building a Supplier Cyber Risk Management Framework
A strong framework includes:
- Supplier risk scoring
- Cyber audits
- Compliance checks
- Incident response plans
- Regular supplier reviews
Addressing vendor risk comprehensively can prevent significant financial losses.
This ensures every vendor meets your organisation’s security expectations.
How ERPSM Helps African Businesses Strengthen Supply Chain Cybersecurity
Staying informed about vendor risk trends can enhance security measures.
Effective supplier verification is essential in managing vendor risk.
ERPSM provides specialised cybersecurity and procurement training designed for African organisations, including:
- Cybersecurity awareness for procurement teams
- Supplier risk management training
- Fraud detection and prevention workshops
- Digital procurement security programmes
- Corporate advisory services
Our programmes help organisations:
- Reduce cyber risk
- Strengthen supplier controls
- Improve compliance
- Protect financial transactions
- Build resilient procurement systems
FAQ: Supply Chain Cybersecurity
1. What is supply chain cybersecurity?
It protects organisations from cyber threats that enter through vendors, suppliers, and procurement systems.
2. Why are African supply chains vulnerable?
Many suppliers lack strong cybersecurity controls, making them easy targets for attackers.
3. What are the most common supply chain cyber threats?
Vendor impersonation, invoice fraud, compromised supplier systems, and procurement platform breaches.
4. How can procurement teams reduce cyber risk?
By verifying suppliers, using MFA, adding cybersecurity clauses to contracts, and undergoing cybersecurity training.
5. How does ERPSM support supply chain cybersecurity?
ERPSM provides training, advisory services, and risk management frameworks to help organisations secure their procurement and vendor ecosystems.
Cyber risk awareness training also addresses vendor risk management.
Related Posts

Cybersecurity Training Explained | Protect Your Business from Within
Spot the Fake: How South African SMEs Can Prevent Cloning Cyber Attacks in 2026

Cyber Risk
Understanding vendor risk is key to maintaining secure operations.
Regular assessments help identify vendor risk factors.
Investing in vendor risk management tools is recommended.
Our training programs emphasize reducing vendor risk across the supply chain.
Organizations must prioritize vendor risk management to avert crises.Identify & Fix Security Gaps | Vulnerability Assessments for Businesses
Related Posts

Cybersecurity Training Explained | Protect Your Business from Within
Spot the Fake: How South African SMEs Can Prevent Cloning Cyber Attacks in 2026

Cyber Risk
Organisations must not overlook vendor risk during their cybersecurity evaluations.
Addressing Vendor Risk for Sustainable Supply Chain Success
Understanding the Impact of Vendor Risk on Supply Chain Efficiency
Related Posts

Cybersecurity Training Explained | Protect Your Business from Within
Spot the Fake: How South African SMEs Can Prevent Cloning Cyber Attacks in 2026