The Supply Chain Is Now the Biggest Cybersecurity Weak Point
The landscape of cybersecurity is continually evolving, and as the reliance on third-party vendors increases, so does the need for robust vendor risk management practices. Organizations should understand the various risks associated with vendor engagements, which can often be overlooked.
For example, a small software vendor with limited security resources could potentially expose your organization to data breaches if they are not adequately assessed. It’s vital to conduct thorough due diligence before onboarding any vendor to understand their security posture.
Additionally, organizations should consider implementing a tiered risk assessment approach based on the sensitivity of the data that vendors will handle. Higher-risk vendors should undergo more rigorous security evaluations and ongoing monitoring.
Moreover, ensuring that vendors regularly update their security measures and protocols is essential, as cyber threats are constantly changing. Regular communication with vendors about their cybersecurity efforts fosters a culture of transparency and trust.
Organizations should also explore cybersecurity insurance policies that cover third-party vendor breaches. This can help mitigate financial losses resulting from vendor-related incidents.
As the digital landscape continues to expand, the need for comprehensive vendor risk management strategies becomes even more critical. Without these strategies, organizations risk not only financial loss but also damage to their reputation.
More than 60% of cyber breaches originate from third‑party vendors, according to global threat intelligence. In South Africa, this risk is amplified by POPIA obligations, outsourced IT services, cloud adoption, and complex supplier ecosystems.
Accountability is another key component in vendor risk management. Organizations must ensure that their vendors are held to the same cybersecurity standards expected internally. This may involve including specific cybersecurity clauses in contracts with vendors.
Vendors should also be required to provide proof of their cybersecurity training programs. This demonstrates their commitment to maintaining a secure environment and reinforces the message that cybersecurity is a priority.
Most organisations invest heavily in internal cybersecurity — but attackers increasingly target vendors, contractors, and service providers with weaker controls. Once a supplier is compromised, the attacker uses that access to infiltrate the primary organisation.
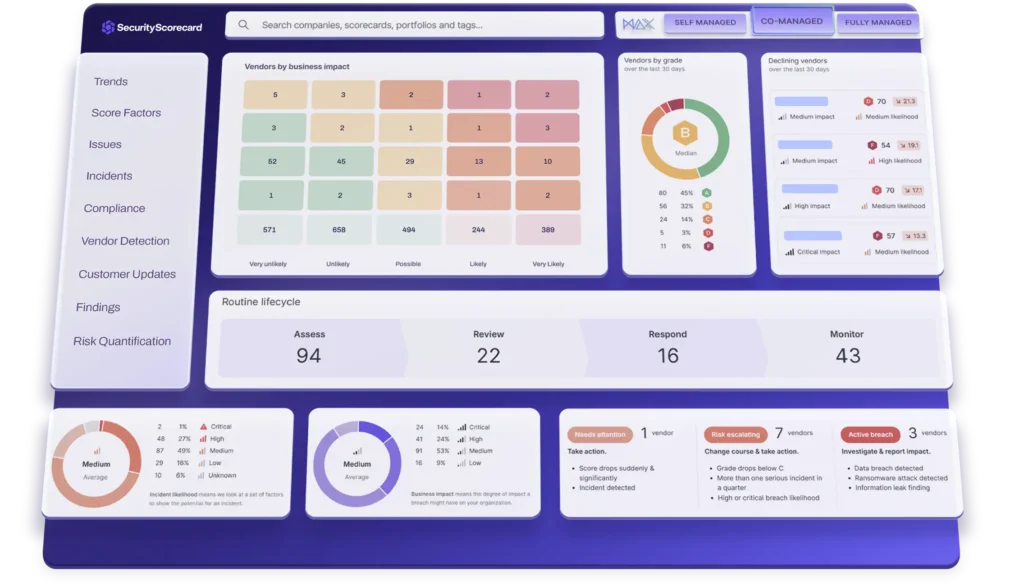
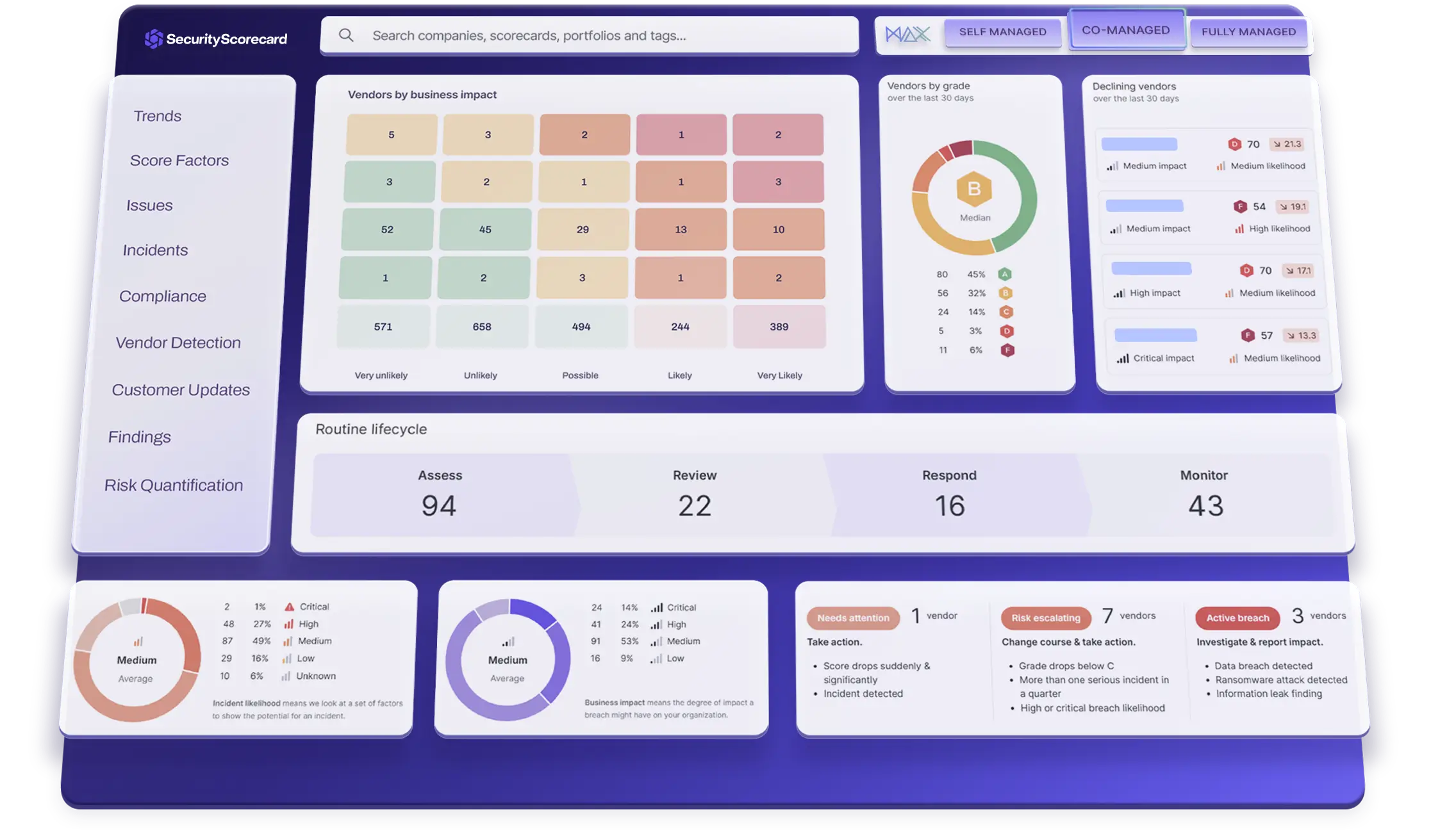
This is why ERP Software Management (ERPSM) uses SecurityScorecard, the world’s leading cyber‑risk rating platform, to help organisations continuously monitor, measure, and reduce vendor‑driven cyber threats.
This highlights the importance of vendor risk management in today’s interconnected business environment, as effective vendor risk management is crucial to mitigate potential breaches.
Why Vendor Breaches Are Increasing
Furthermore, organizations should invest in training their employees about vendor risk management. Educating staff about the potential risks associated with third-party vendors can help create a more security-aware culture within the organization.
Continually reviewing and updating vendor risk management policies is essential to adapt to the evolving threat landscape. Organizations must be proactive in addressing new risks that may arise from changes in vendor operations or the regulatory environment.
To further support compliance with POPIA, it is beneficial for organizations to conduct regular audits on their vendors. Audits can help identify gaps in security practices and enforce compliance with data protection regulations.
Engaging with vendors in joint cybersecurity initiatives can also enhance security for both parties. Collaborative efforts, such as shared training sessions or joint incident response exercises, can strengthen the security posture of the entire supply chain.
1. Vendors Often Have Weaker Cybersecurity Controls
Many suppliers lack:
- strong patching practices
- endpoint protection
- secure configurations
- phishing‑resistant processes
Attackers exploit the weakest link — and that link is often a vendor.
2. POPIA Makes You Liable for Vendor Breaches
Under POPIA, organisations are legally responsible for breaches caused by third‑party processors handling personal information. If your vendor is breached, you face the penalties.
3. Lack of Continuous Monitoring
Most organisations rely on:
As part of a comprehensive vendor risk management strategy, organizations might also consider implementing third-party security assessments. By utilizing third-party security professionals to evaluate vendor security measures, organizations can gain an objective perspective on potential vulnerabilities.
Using tools such as SecurityScorecard, organizations can obtain a clearer picture of their risk exposure regarding vendors. This actionable insight allows them to prioritize their risk management efforts effectively.
- annual questionnaires
- outdated spreadsheets
- manual vendor assessments
But cyber risk changes daily. A vendor that was secure last month may be compromised today.
How ERPSM Reduces Vendor Cyber Risk Using SecurityScorecard
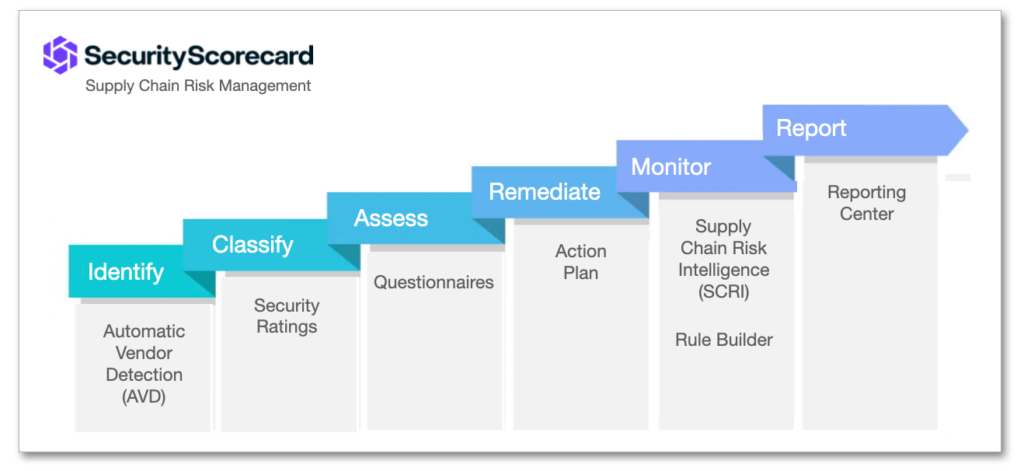
ERPSM delivers a complete Third‑Party Risk Management (TPRM) solution powered by SecurityScorecard’s real‑time cyber‑risk intelligence.
1. Real‑Time Vendor Cyber Risk Ratings
SecurityScorecard provides A–F security ratings for every supplier across 10 risk categories, including:
- network security
- DNS health
- application security
- endpoint security
- IP reputation
- patching cadence
ERPSM uses these ratings to help organisations identify high‑risk vendors instantly.
Additionally, organizations should establish clear benchmarks and metrics for evaluating vendor performance in terms of cybersecurity. This will aid in identifying which vendors may require more attention or support in their security practices.
2. Continuous Monitoring of All Suppliers
Instead of annual reviews, ERPSM enables:
- daily monitoring
- automated alerts
- risk trend analysis
- early detection of vulnerabilities
This ensures organisations always know which vendors pose immediate risk.
3. POPIA & SARB Compliance Support
SecurityScorecard helps organisations demonstrate:
- due diligence
- vendor oversight
- continuous monitoring
- risk remediation tracking
It’s also important to ensure that vendor contracts contain proper incident response protocols. These protocols should outline the responsibilities of both parties in the event of a data breach or security incident.
ERPSM aligns this with POPIA, SARB Outsourcing Guidelines, and global TPRM standards.
4. Vendor Engagement and Remediation
ERPSM helps organisations:
- share findings with vendors
- request remediation
- track improvements
- strengthen supplier security posture
This builds a more secure supply chain ecosystem.
Security Scorecard
- vendor cyber risk
- SecurityScorecard South Africa
- third‑party risk management
- ERPSM cybersecurity
- why 60% of breaches come from vendors
- SecurityScorecard vendor monitoring South Africa
- POPIA third‑party risk compliance
- how to reduce supplier cyber risk
- continuous vendor cyber risk ratings
Final Thoughts on Vendor Risk Management
In the rapidly changing digital landscape, organizations must prioritize vendor risk management. Implementing effective strategies not only protects sensitive information but also reinforces the security of the entire supply chain. By continuously monitoring vendor performance and addressing potential vulnerabilities, businesses can mitigate risks associated with third-party vendors.
Why do most breaches come from vendors?
Because attackers target suppliers with weaker cybersecurity controls, then use that access to infiltrate larger organisations.
How does SecurityScorecard help reduce vendor cyber risk?
SecurityScorecard provides real‑time cyber‑risk ratings, continuous monitoring, and automated alerts that help organisations identify and remediate supplier vulnerabilities.
How does ERPSM use SecurityScorecard?
ERPSM integrates SecurityScorecard into a full TPRM programme that includes monitoring, compliance support, vendor engagement, and remediation tracking.
Is vendor risk part of POPIA compliance?
Finally, organizations should leverage technology to automate some aspects of vendor risk management. Tools that streamline assessment processes and monitor vendor performance can significantly enhance the efficiency of risk management efforts.
Yes. POPIA requires organisations to ensure that third‑party processors handling personal information maintain adequate security controls.
Ultimately, a proactive approach to vendor risk management not only protects organizations from potential breaches but also fosters stronger relationships with vendors, contributing to a more resilient supply chain.
In conclusion, as businesses continue to rely on vendor partnerships, prioritizing robust vendor risk management practices will be essential in safeguarding sensitive information and maintaining compliance in an ever-changing regulatory landscape.
The emphasis on vendor risk management will only grow stronger as cyber threats evolve. Organizations that invest in their vendor risk management processes today will be better positioned to face the challenges of tomorrow.
Related Posts

Supply Chain Cybersecurity: How African Businesses Can Protect Their Vendors, Data, and Procurement Systems in 2026

Protect Your Business Ecosystem | Security Scorecard for Third-Party Risk





3 Responses