The vulnerability assessment is a testing procedure intended to locate and rate the seriousness of as many security flaws as feasible in a predetermined amount of time. This procedure could include both automatic and manual methods, with different rigor levels and a focus on thorough coverage. Vulnerability assessments may focus on various technological layers using a risk-based methodology, with host-, network-, or application-layer assessments being the most popular.
Before a compromise occurs, vulnerability testing enables organizations to find weaknesses in their technology and underlying architecture. A software vulnerability is defined as follows, though.
Read Also: Cyber Monitoring
There are two ways to characterize a vulnerability
- A software design defect or a bug in the code can be used to harm users. The vulnerability may involve a verified or unverified attacker.
- A flaw in internal controls or a security mechanism that, when exploited, leads to a breach of security.
What is the process of a vulnerability analysis?
An evaluation of vulnerabilities has three main goals.
- Locate vulnerabilities, ranging from serious design problems to easy configuration errors.
- Identify the vulnerabilities and document them so that programmers can quickly recognize and replicate the results.
- Produce instructions to help developers fix the discovered flaws.
The process of vulnerability testing might be varied. Technological Devices Security Testing is one approach (DAST). By supplying inputs or other failure conditions to detect flaws in real time, DAST is a dynamic analysis testing technique that involves operating an application (most frequently a Web application). It is used primarily to identify security flaws. Static application security testing (SAST), on the other hand, entails the study of an application’s source code or object code in order to find vulnerabilities without executing the programme.
The two techniques take quite distinct approaches to applications. They can identify different kinds of vulnerabilities and are most useful at various stages during the software development product lifecycle. Cross-site scripting (XSS) or SQL injection, for instance, are major vulnerabilities that SAST identifies earlier in the SDLC. While Web apps are being used, DAST employs an outside-in penetrating testing strategy to find security flaws.
Penetration testing, which is a form of vulnerability analysis in and of itself, involves goal-oriented security testing. Penetration testing targets one or more particular goals while putting a strong emphasis on an exploratory approach (simulating an attacker’s techniques).
Assessment of vulnerabilities: Security inspection procedure.
Four steps make up the security scanning process: testing, analysis, evaluation, and remedy.
1. Identification of vulnerabilities
This step’s goal is to create a thorough inventory of an app’s risks. By using automated methods to scan them or actively testing and assessing them, security analysts can determine whether applications, servers, or other systems are secure. To find security flaws, analysts also use vulnerability registries, vendor vulnerability bulletins, asset management systems, and threat intelligence feeds.
2. Analysis of vulnerabilities
Finding the source and root problem of the vulnerabilities found in step one is the goal of this stage.
It entails determining the system elements and vulnerability’s underlying cause for each vulnerability. For instance, an outdated free software library could be the cause of a vulnerability. This offers a direct route for corrective action—upgrading the library.
3. Risk evaluation
Prioritizing vulnerabilities is the goal of this phase. Each vulnerability is given a ranking or intensity score by security experts based on a variety of criteria, including:
- Which data is in danger.
- Which business processes are in danger.
- Ease of compromise or assault.
- The intensity of an assault.
- Damage that could come from the vulnerability
4. Correction
The closure of security gaps is the goal of this step. Security personnel, technical staff, and operational processes often work together to decide the best course of action for fixing or mitigating each vulnerability.
The following specific corrective actions could be taken:
- Implementation of new security protocols, controls, or technologies.
- The upgrading of configuration or operational modifications.
- Creating and deploying a vulnerability patch.
Assessment of vulnerabilities cannot be a one-time task. Organizations must implement this approach and carry it out repeatedly for it to be effective. Additionally, it is essential to promote DevSecOps, or development, operations, and security team collaboration.
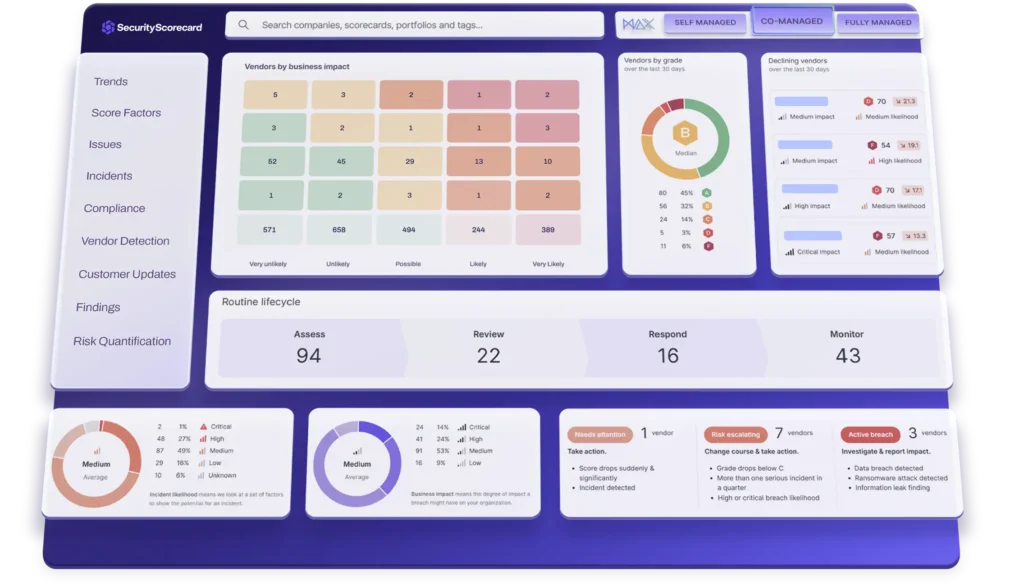
Tools for evaluating vulnerabilities
Tools for vulnerability assessment are made to automatically search for potential risks to your application, both new and old. Web app analyzers that test for something and mimic well-known attack patterns are one example of a tool type.
Protocol detectors look for network services, ports, and protocols that are weak.
Network scanners aid in network visualization and find warning signs such as errant IP addresses, faked packets, and abnormal packet production from a single IP.
Scheduling routine, automated assessments of all crucial IT systems is great practice. These scans’ findings must be incorporated into the company’s continuous vulnerability assessment procedure.