How Weak Third‑Party Risk Management Has Exposed African Organisations to Cyber Attacks
Across Africa, cyber attacks linked to third‑party suppliers, IT vendors, and outsourced service providers have increased sharply. Weak Third‑Party Risk Management (TPRM) has become one of the top causes of data breaches, financial loss, and operational disruption. As organisations digitise procurement, finance, HR, and supply chain systems, attackers increasingly exploit supplier vulnerabilities to gain access. […]
The Rise of AI‑Powered Cyber Attacks in South Africa: What SMEs Must Know in 2026

South Africa is experiencing a surge in AI‑powered cyber attacks, with SMEs becoming the primary target. As cybercriminals adopt machine learning, automation, and deepfake technology, traditional security tools are no longer enough. In 2026, South African businesses face a new wave of threats that are faster, smarter, and more damaging than anything seen before. Integrating […]
Why 60% of Breaches Come from Vendors — And How ERPSM Reduces That Risk (Security Scorecard)
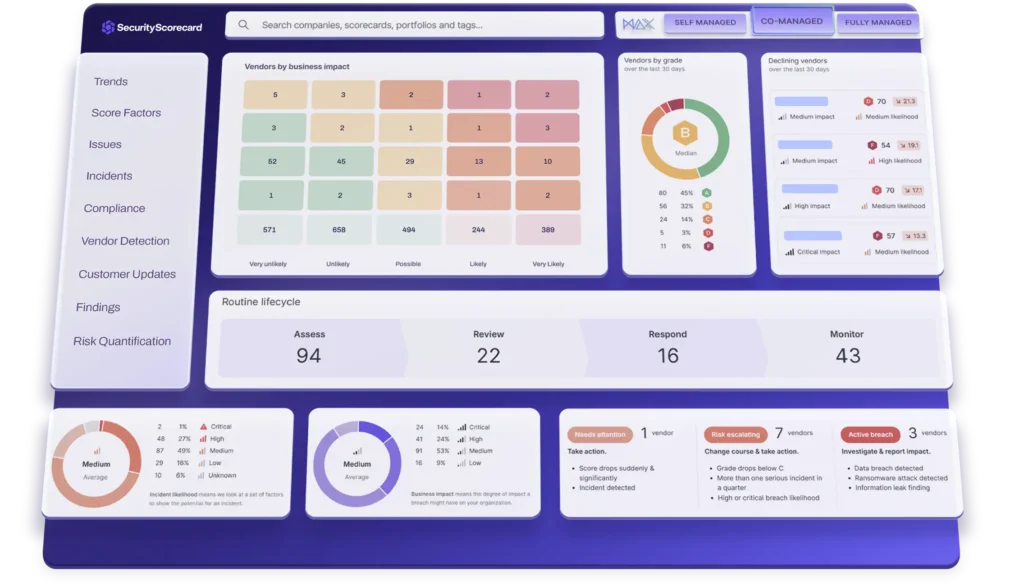
The Supply Chain Is Now the Biggest Cybersecurity Weak Point The landscape of cybersecurity is continually evolving, and as the reliance on third-party vendors increases, so does the need for robust vendor risk management practices. Organizations should understand the various risks associated with vendor engagements, which can often be overlooked. For example, a small software […]
What Is Managed Security Services (MSS)? A Simple Guide for South African Businesses

South African businesses face rising cyber threats, limited internal IT capacity, and increasing compliance pressure. Managed Security Services (MSSP) offer a smarter, more cost‑effective way to protect your organisation. This guide explains what Managed Security Services are, why they matter, and how MSSP helps South African companies stay secure and compliant. By utilizing security services, […]
Supply Chain Cybersecurity: How African Businesses Can Protect Their Vendors, Data, and Procurement Systems in 2026

Why Supply Chain Cybersecurity and Vendor Risk Are Critical for African Businesses in 2026 Understanding Vendor Risk in African Supply Chains As businesses navigate this landscape, managing vendor risk becomes increasingly crucial. Managing vendor risk effectively is essential for maintaining a resilient supply chain. Africa’s digital transformation is accelerating — but so are cyberattacks targeting […]
Spot the Fake: How South African SMEs Can Prevent Cloning Cyber Attacks in 2026
Cloning cyber attacks are rising sharply across South Africa, targeting SMEs with fake websites, cloned WhatsApp accounts, impersonated emails, and fraudulent payment requests. In 2026, cybercriminals are using AI‑powered cloning tools to mimic brands, executives, suppliers, and even entire ERP portals. South African SMEs—already vulnerable due to limited cybersecurity budgets—are now facing a new wave […]
Cloud Security Training by ERP: A detailed overview

Importance of Cloud Security Training Ultimately, Cloud Security Training equips individuals with the necessary skills to tackle current security challenges. In conclusion, Cloud Security Training is a crucial element for any organization leveraging cloud technologies. Participating in Cloud Security Training fosters a culture of security within organizations. One of the critical components is understanding the […]
Strengthen Your IT Security Posture | Cybersecurity for IT Teams

Introduction In today’s tech-savvy world, where we’re all connected through computers, smartphones, and the internet, the importance of cybersecurity practices in the field of Information Technology (IT) cannot be stressed enough. Imagine a fortress that protects all our digital stuff like sensitive data, important systems, and even our personal secrets from sneaky cyber bad guys. […]
Enhancing Cybersecurity Measures in the Education Department

Strengthening Cybersecurity in the Education Sector: 5 Essential Measures for 2026 The education sector has become one of the fastest‑growing targets for cyberattacks in 2026. Schools, colleges, and education departments store sensitive data — from student records to financial information — making them attractive to cybercriminals. As digital learning expands across Africa, strengthening cybersecurity in […]
Implementing Zero Trust Security | Best Practices for South African Enterprises

Zero trust security is a cyber security framework that emphasizes the concept of “trust no one” when it comes to network security. It is designed to protect digital assets and data by assuming that no user or device should be inherently trusted, regardless of their location or network access. Traditionally, network security has relied on […]
Zero Trust Microsegmentation for Advanced Network Security

Network security is a critical concern for organizations of all sizes and industries, and ERP Software Management understands the importance of providing its customers with the best possible security solutions. With the growing complexity of networks and the increasing sophistication of cyber threats, it has become essential to adopt a zero-trust security architecture that provides […]
Next Generation Endpoint Protection Platform | Cybersecurity for 2026

The increasing complexity of cyber threats has made it imperative for organizations to adopt advanced cybersecurity solutions that can adapt to the ever-changing threat landscape. SentinelOne’s advanced endpoint protection platform incorporates state-of-the-art technologies that enable organizations to effectively detect, respond to, and neutralize even the most advanced cyber attacks. For example, organizations that have implemented […]
Boost Your Career with ERP Software Management’s PECB Training and Certification
Boost Your Career with ERP Software Management’s PECB Training and Certification In today’s digital age, companies are always finding ways to improve their performance and stay up to date. One of the most essential tools for achieving this is ERP Software Management PTY LTD, the greatest provider of services and solutions with its authorized partnership […]
SAP Audit Services for ERP Systems: How Audits Improve Security, Compliance, and System Performance

SAP (Systems, Applications, and Products) is one of the world’s most powerful ERP platforms, enabling organizations to integrate finance, procurement, logistics, HR, production, and reporting into one unified system. But as SAP environments expand, so do the risks — cyber threats, compliance failures, data exposure, and operational inefficiencies. This is why SAP Audit Services have […]
What Is Endpoint Security? A Guide for South African Businesses

In today’s digital age, endpoint security has become more important than ever. With cyber threats on the rise and remote work becoming the norm, organizations must prioritize protecting their endpoints from attacks that can compromise sensitive data and put their entire network at risk. By implementing effective endpoint security measures, organizations can ensure the safety […]
Affordable IT Certification in South Africa | CompTIA Training & Vouchers

Get Globally Recognised Certifications at the Best Prices in South Africa. CompTIA certifications are essential for anyone looking to establish a career in IT. We emphasize the importance of CompTIA certifications in our training programs. CompTIA offers a variety of courses suitable for different career paths. If you’re looking for affordable, accredited, and career‑boosting IT […]
What is network security?

What is network security? Network security involves preventing unwanted access, misuse, and theft of the core network connection. In order for users, apps, devices, and other parties to work securely, a secure infrastructure must be built. Network security comprises numerous levels of protection, both inside the network and around its edges. Policies and controls are […]
Automated Penetration Testing in South Africa | POPIA-Compliant Security
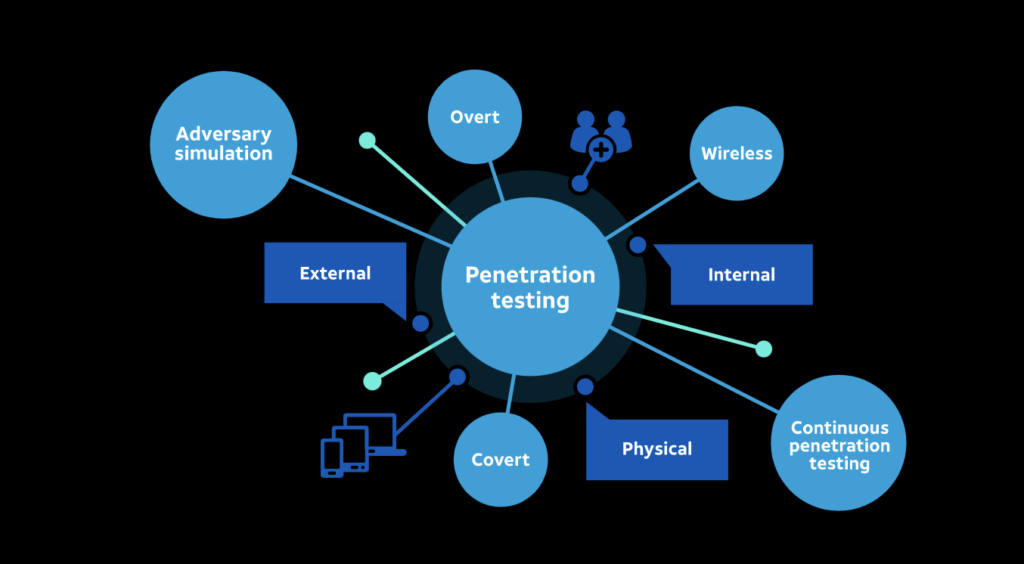
We should first quickly describe penetration testing before we can discuss automated vulnerability scanning. A penetrating test is a procedure where a knowledgeable security tester looks for vulnerabilities and tries to compromise the protection of your assets. This is exactly what computerized penetration testing is, correct? Yeah, kind of, maybe. In practice, penetration testing includes […]
What is a Cloning Cybersecurity?

What is a Cloning Cybersecurity Cybercriminals utilize cloning cybersecurity, often known as phishing, to trick their targets into believing a harmful email looks similar to a genuine one. Clone scam assaults are typically significantly more difficult for unwary people to spot since they resemble authentic emails. But, by having a deeper grasp of clone phishing, […]
Cyber Risk

We can clearly see the possibilities and challenges that come with digital technology, devices, and media. Cyber risk is never just an IT staff concern. Detailed knowledge of the continuously changing hazards is essential for the risk management role of an organization. In addition to the useful tools and approaches, the ability to solve them […]

