Introduction
The proliferation of cloud computing has revolutionized how businesses operate, offering unparalleled flexibility, scalability, and efficiency. However, this transformation also introduces a new realm of security challenges. As organizations transition critical data and applications to cloud environments, ensuring robust cloud security has become a top priority. Cloud security training is pivotal in equipping individuals and businesses with the skills to protect their assets and sensitive information in the cloud.
Read More: Cybersecurity in IT department
Key Aspects of Cloud Security Training
Cloud Architecture and Design: Understanding the architecture and design of cloud environments is fundamental. Participants learn how cloud services are structured, including components like virtualization, storage, networking, etc. This knowledge forms the basis for implementing secure cloud solutions.
Identity and Access Management (IAM): IAM is a core cloud security component. Training covers managing user identities, roles, and permissions within the cloud environment. This ensures that only authorized individuals can access resources and data.
Data Security: Protecting data at rest, in transit, and during processing is crucial. Cloud security training explores encryption techniques, data masking, tokenization, and secure data storage practices to prevent unauthorized access and data breaches.
Network Security: Participants learn to design secure network architectures for cloud environments. This includes techniques like network segmentation, firewalls, intrusion detection, and intrusion prevention systems.
Endpoint security for businesses refers to protecting devices such as laptops, desktops, servers, and mobile devices that connect to company systems or cloud environments. In South Africa, strong endpoint security helps organizations detect malware, prevent unauthorized access, and stop cyber threats before they spread across the network or cloud infrastructure.
Application Security: Cloud applications need to be developed and deployed securely. Training addresses secure coding practices, vulnerability assessments, and application security testing to identify and rectify potential vulnerabilities.
Compliance and Governance: Cloud environments must often adhere to specific compliance standards and regulations. Training covers aligning cloud security practices with compliance requirements and meeting legal and regulatory obligations.
Risk Management: Understanding and assessing risks is crucial in cloud security. Training provides insights into risk assessment methodologies, threat, modelling and risk mitigation strategies to make informed decisions about security measures.
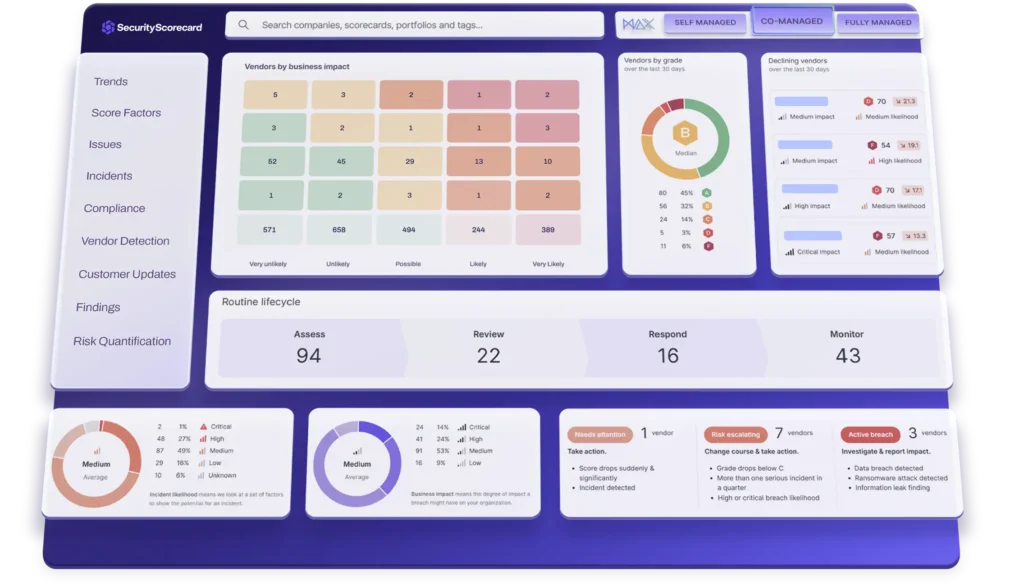
Security Monitoring and Incident Response: Participants learn to monitor cloud environments for suspicious activities and potential breaches. Incident response training prepares individuals to react swiftly and effectively in a security incident.
Cloud Provider Security: Cloud services operate under a shared responsibility model, where the provider and the customer have security responsibilities. Training helps individuals understand their responsibilities within this model and how to work collaboratively with cloud providers.
Multi-Cloud and Hybrid Environments: A lot of businesses work in these types of settings. Training covers the challenges and best practices for maintaining security across various cloud platforms.
Cloud Security Best Practices: Participants gain insights into industry-recognized best practices for cloud security. This includes least privilege, continuous monitoring, and secure configuration management.
Emerging Threats: Cloud security training keeps professionals up-to-date with the latest trends in cyber threats targeting cloud environments. This knowledge enables proactive measures to counter emerging security challenges.
Security Automation and Orchestration: As cloud environments scale, automation becomes vital. Training covers security automation and orchestration tools and techniques to streamline security operations.
Business Continuity and Disaster Recovery: Ensuring business continuity in disruptions is vital. Training addresses designing and implementing adequate disaster recovery plans for cloud environments.
Here are some key benefits of cloud security training:
Enhanced Expertise: Cloud security training provides individuals with a deep understanding of cloud security principles, best practices, and emerging threats. This expertise enables them to effectively design, implement, and manage secure cloud environments.
Reduced Vulnerabilities: Trained professionals can identify vulnerabilities and security gaps within cloud infrastructures. Applying proper security measures and controls can significantly reduce the risk of data breaches and cyberattacks.
Improved Compliance: Cloud security training covers regulatory frameworks and compliance requirements specific to different industries and regions. This knowledge empowers professionals to implement security measures that align with these standards, avoiding legal and regulatory complications.
Effective Risk Management: Understanding risk assessment methodologies and threat landscapes enables trained individuals to assess and prioritize risks accurately. This results in better-informed decisions regarding risk mitigation strategies.
Swift Incident Response: In the event of a security incident, trained professionals are better equipped to respond swiftly and effectively. They can follow established incident response protocols, minimizing the impact of the breach and facilitating a faster recovery.
Adaptation to Evolving Threats: Cloud security training keeps professionals updated with the latest trends in cyber threats and attack vectors targeting cloud environments. This knowledge ensures that security measures remain relevant and practical.
Strategic Cloud Implementation: Trained experts can guide organizations in selecting appropriate cloud service models and deployment options based on security requirements. This ensures that security considerations are integrated into the overall cloud strategy.
Cost Savings: Investing in cloud security training can save substantial costs by preventing potential security breaches. The financial losses and reputational damage resulting from a breach can far outweigh the costs of proactive training.
Cross-Disciplinary Skills: Cloud security training often touches various cybersecurity domains, including encryption, access management, network security, and more. This provides professionals with a broader skillset that can be applied across different security areas.
Career Advancement: Individuals who complete cloud security training enhance their professional profiles and increase their employability. The certification earned through training can serve as a validation of their skills and dedication to cloud security.
Organizational Resilience: Well-trained cloud security professionals contribute to the overall resilience of an organization’s IT infrastructure. They are crucial in maintaining business continuity and minimizing downtime during security incidents.
Industry Recognition: Cloud security training often leads to industry-recognized certifications. These certifications validate a professional’s expertise and can open new career opportunities.
In a digital landscape where cyber threats constantly evolve, cloud security training is an essential investment for individuals and businesses. It empowers professionals to secure cloud environments proactively, adapt to emerging challenges, and contribute to building a safer and more resilient digital future.
Why cloud security training aligns uniquely with your profile and aspirations:
Tech-Savvy Foundation:
Your existing tech-savvy nature lays a strong foundation for grasping cloud security concepts effectively. Your familiarity with technology enhances your ability to navigate complex security protocols and understand their practical implications.
Holistic Skill Integration: Your multi-disciplinary background uniquely positions you to grasp the broader impact of cloud security. Integrating your diverse knowledge, from coding to system administration, will enable you to approach cloud security holistically.
Innovative Mindset: Cloud security often demands innovative solutions due to its rapidly evolving nature. Your creative mindset equips you to think creatively when devising security strategies that can adapt to emerging threats and challenges.
Effective Communication: The ability to communicate complex technical concepts clearly and relatable sets you apart. This skill is invaluable when collaborating with colleagues, clients, or stakeholders needing a technical background.
Cross-Domain Adaptability: Your experience across multiple domains grants you unique adaptability. This quality is particularly advantageous in cloud security, where the convergence of technology and business considerations requires professionals who can bridge the gap.
Problem-Solving Aptitude: Cloud security often presents intricate challenges that require adept problem-solving. Your track record of tackling complex issues positions you to excel in analyzing security vulnerabilities and devising effective countermeasures.
Data Privacy Advocacy: Your passion for data privacy aligns seamlessly with the core tenets of cloud security. This synergy allows you to approach cloud security as a technical task and as a mission to safeguard sensitive information.
Risk Management Perspective: Your background in risk assessment lends itself well to cloud security. You possess the insight to identify potential risks, assess their impact, and effectively make informed decisions to mitigate them.
Industry Niche Expertise: Your expertise in specific industries further enriches your cloud security journey. You can tailor security measures to align with industry-specific regulations and nuances, offering a nuanced approach to protection.
Future-Proofing Skills: Cloud security is a dynamic field with continuous advancements. Your commitment to lifelong learning lets you stay updated with the latest trends, ensuring your skills remain relevant and practical.
Leadership Potential: Your leadership experience equips you to excel as a cloud security professional and guide teams and organizations toward enhanced security practices, setting a proactive example.
Ethical Stance: Your ethical considerations set a solid moral compass, aligning with the ethical responsibilities inherent in cloud security. Your commitment to doing what is right complements the ethical dimensions of the field.
User-Centric Approach: With a user-centric approach, you prioritize user experience while implementing security measures. This balance is essential in cloud security, where usability and protection must coexist.
Global Perspective: Exposure to diverse cultures and environments brings a global perspective to your approach—cloud security, with its international implications, benefits from professionals who understand global nuances.
Choosing the right cybersecurity provider in South Africa requires evaluating the provider’s experience, certifications, service scope, and local support capabilities. Businesses should look for providers that offer comprehensive cloud security training, proactive threat monitoring, compliance knowledge, and scalable solutions that align with their specific risk profile and growth plans.
Conclusion
Cloud security training is essential for individuals and organizations venturing into cloud environments. As the cloud landscape continues to evolve, the ability to protect sensitive information and digital assets is paramount. By undergoing comprehensive cloud security training, individuals gain the knowledge and skills needed to navigate the complexities of cloud security, ensuring a secure and resilient digital future.